Issue
Before April 2022, for onboarding Windows Server 2012 R2 and Windows Server 2016 servers on Microsoft Defender, you had to use Group Policy for applying the security policies. After April 2022, Microsoft added support for the modern unified solution to onboard Windows Server 2012 R2 and Windows Server 2016 to Microsoft Defender. A prerequisite for this is that the servers are (hybrid) joined to the Azure AD and that they are registered in Azure AD.
Here was the problem. The affected Windows Servers were not registered, they remained in the ‘Pending’ status in the Azure AD.
Potential cause
The likely cause of the loss of registration status for these servers, which resulted in them being in a ‘Pending’ state, was due to a temporary removal during a migration path and subsequent resynchronization to Azure AD via Azure AD Connect and a failed Hybrid Device Join process, as the devices already existed in the Azure AD.
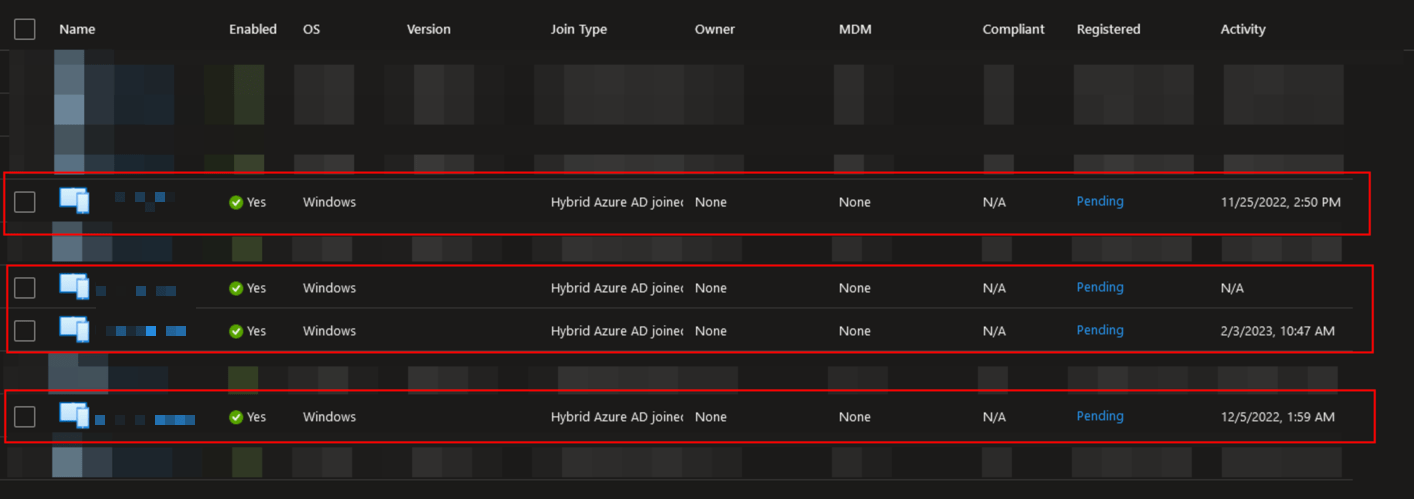 Devices Stuck in Pending state in Azure AD
Devices Stuck in Pending state in Azure AD
Solution
To onboard those servers to Microsoft Endpoint Manager (Microsoft Intune) for applying the Microsoft Defender policies, you have to solve this problem. It’s mandatory for Microsoft Defender that these servers are in the proper registration state.
To trigger a Hybrid Device Join, I had to remove these servers from the Azure AD and rejoin them again. For this, I have followed the following steps:
- Verify that the servers in the are synchronized to the Azure AD in Azure AD Connect.
- Logon to the relevant Windows Server.
- Open the Command Prompt with Administrator privileges.
- To remove the server from the Azure AD, run the following command:
dsregcmd /leave - Check to see if the server has disappeared from AAD. (If necessary, check the Audit Logs indicating that the server has been deleted).
- Reboot the Windows Server.
- After about 10 minutes, the server should be visible again in AAD. After about 90 minutes, the registration process should also be complete, and the registration status will be
registered.
For understanding and solving this problem, the YouTube video below was very valuable.